Cloud Workload Security: Ensuring the Safety of Your Data in the Cloud
As businesses increasingly migrate their data and applications to the cloud, the need for robust security measures to protect sensitive information has never been greater. Cloud workload security refers to the strategies and technologies put in place to safeguard data and workloads in the cloud environment, ensuring that they are protected from cyber threats and unauthorized access.
What do you mean by Cloud Workload Security?
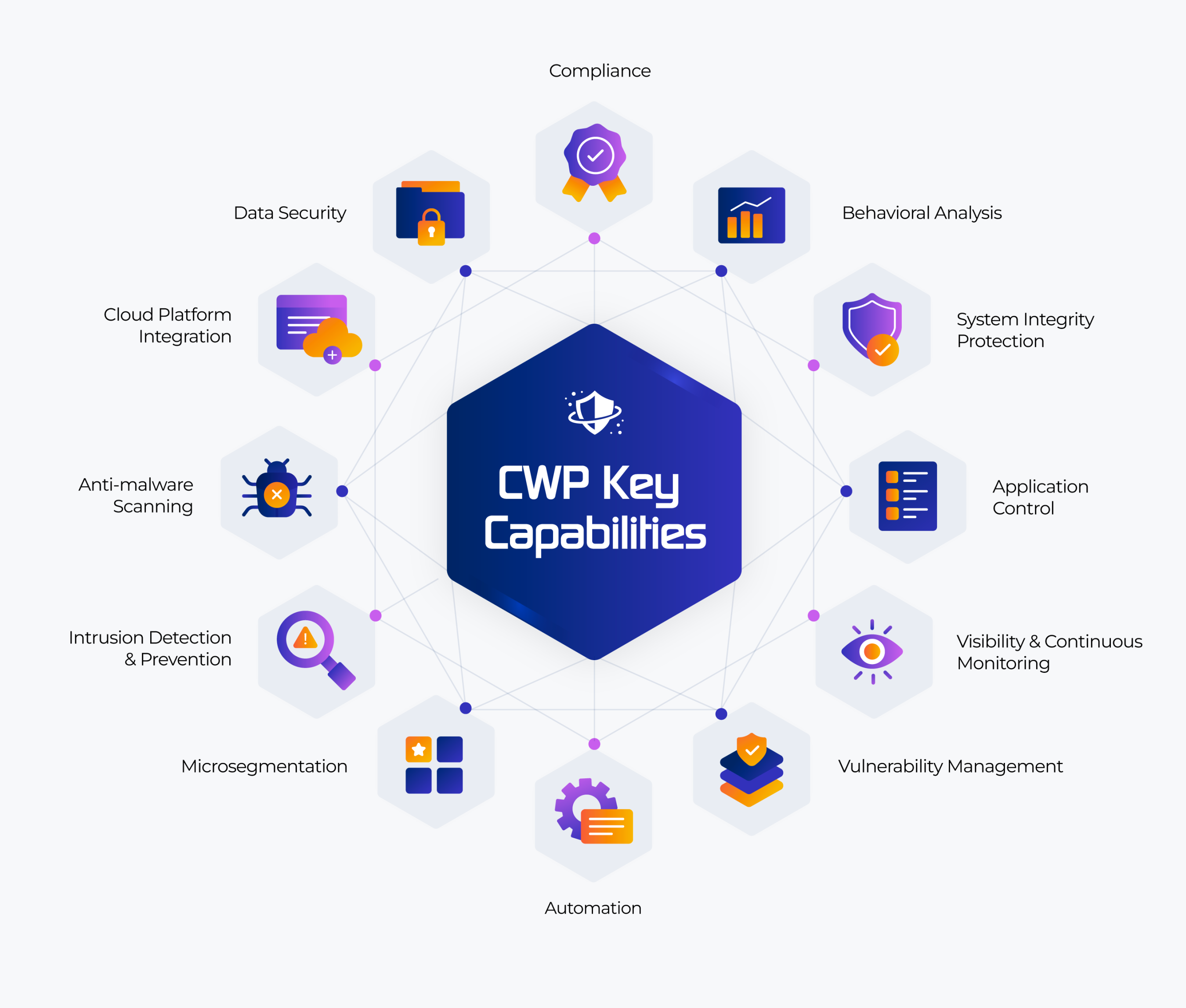
Cloud workload security encompasses a range of measures designed to protect data and workloads in the cloud. This includes encryption, access control, authentication, and monitoring tools that help to detect and respond to potential security threats. By implementing cloud workload security, organizations can ensure that their data remains secure and compliant with regulatory requirements.
How does Cloud Workload Security work?
Cloud workload security works by implementing a combination of technologies and best practices to protect data and workloads in the cloud. This includes encryption to scramble data and make it unreadable to unauthorized users, access control to restrict who can access sensitive information, monitoring tools to detect unusual activity, and authentication mechanisms to verify the identity of users accessing the cloud environment.
What is known about Cloud Workload Security?
Cloud workload security is essential for organizations of all sizes and industries to protect their data and workloads in the cloud. Without adequate security measures in place, data stored in the cloud is vulnerable to cyber attacks, data breaches, and other security threats that can result in financial losses, reputational damage, and compliance violations. By investing in cloud workload security, organizations can mitigate these risks and ensure the safety of their data.
What are the common challenges in Cloud Workload Security?
One of the common challenges in cloud workload security is the complexity of managing security across multiple cloud environments and workloads. As organizations adopt multi-cloud or hybrid cloud strategies, ensuring consistent security policies and controls can be difficult. Additionally, the dynamic nature of cloud environments can make it challenging to detect and respond to security threats in real-time.
What is the Solution to Cloud Workload Security?
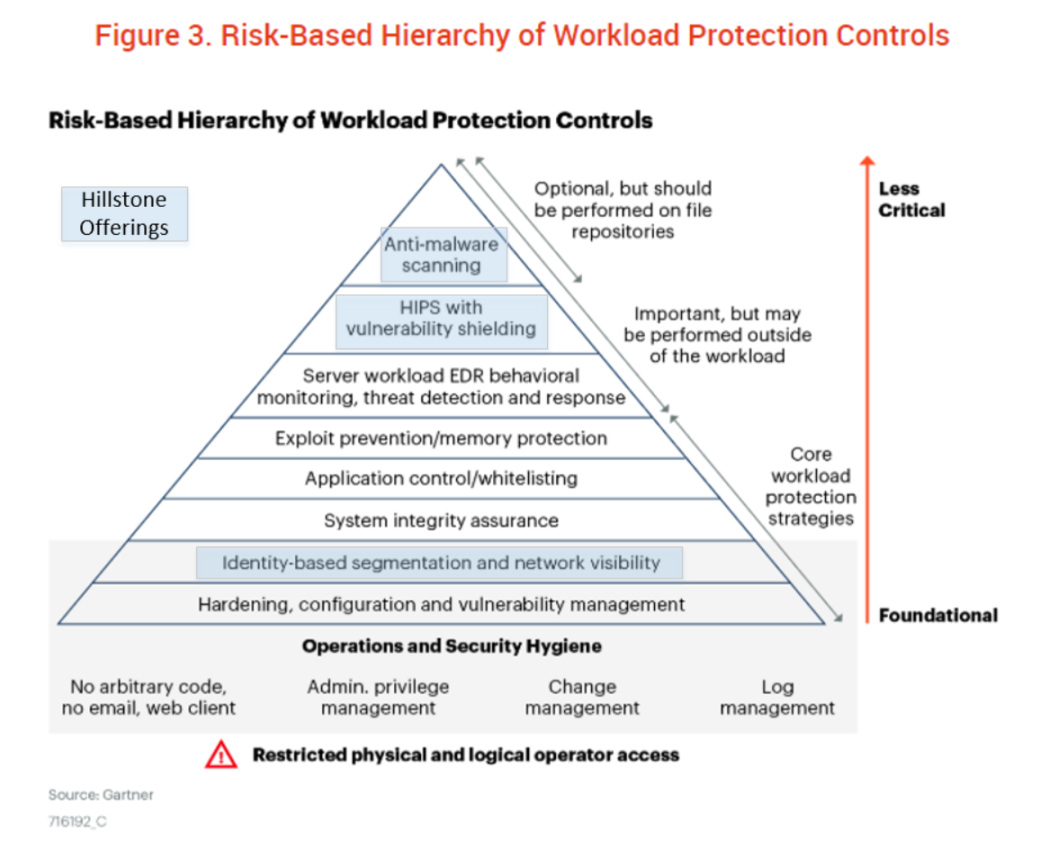
To address the challenges of cloud workload security, organizations need to implement a comprehensive security strategy that includes a combination of technologies, policies, and best practices. This may include deploying encryption and access control mechanisms, implementing continuous monitoring and threat detection tools, and conducting regular security audits and assessments to identify and address vulnerabilities in the cloud environment.
Why is Cloud Workload Security important?
Cloud workload security is important because it helps organizations protect their data and workloads in the cloud from cyber threats and unauthorized access. With the increasing number of cyber attacks targeting cloud environments, organizations need to prioritize security to safeguard their sensitive information and maintain the trust of their customers and partners. By investing in cloud workload security, organizations can reduce the risk of data breaches and ensure the integrity and confidentiality of their data.
How can organizations improve Cloud Workload Security?
Organizations can improve cloud workload security by implementing a defense-in-depth approach that includes multiple layers of security controls to protect data and workloads in the cloud. This may include deploying encryption and access control mechanisms, implementing network segmentation and isolation, monitoring and logging all activities in the cloud environment, and educating employees on best security practices.
Conclusion
In conclusion, cloud workload security is essential for organizations to protect their data and workloads in the cloud environment. By implementing robust security measures and best practices, organizations can safeguard their sensitive information from cyber threats and unauthorized access, ensuring the integrity and confidentiality of their data. Investing in cloud workload security is crucial for organizations to maintain the trust of their customers and partners and mitigate the risks associated with storing data in the cloud.
FAQs
1. What are the key components of cloud workload security?
The key components of cloud workload security include encryption, access control, monitoring tools, authentication mechanisms, and security policies and procedures.
2. How can organizations ensure compliance with regulatory requirements in the cloud?
Organizations can ensure compliance with regulatory requirements in the cloud by implementing security controls and practices that align with industry standards and regulations, conducting regular security audits and assessments, and documenting their security measures.
3. What are the benefits of investing in cloud workload security?
The benefits of investing in cloud workload security include reducing the risk of data breaches, protecting sensitive information from cyber threats, maintaining compliance with regulatory requirements, and maintaining the trust of customers and partners.
4. How can organizations address the challenges of managing security in multi-cloud environments?
Organizations can address the challenges of managing security in multi-cloud environments by adopting a centralized security management approach, implementing security automation and orchestration tools, and enforcing consistent security policies and controls across all cloud environments.
5. What are some best practices for ensuring cloud workload security?
Some best practices for ensuring cloud workload security include implementing strong encryption for data at rest and in transit, regularly updating security patches and software, conducting employee security training, implementing access control and least privilege principles, and monitoring and auditing all activities in the cloud environment.



