Cloud Security Posture Management Gartner Magic Quadrant
What do you mean by Cloud Security Posture Management?
Cloud Security Posture Management (CSPM) is a set of security tools and policies designed to help organizations secure their cloud environments. It involves continuous monitoring and assessment of cloud infrastructure to ensure compliance with security best practices and regulatory requirements. CSPM solutions provide visibility into cloud assets, identify misconfigurations and vulnerabilities, and help remediate security risks.
How does Cloud Security Posture Management work?
CSPM solutions use a combination of automated tools and manual processes to monitor cloud environments for security risks. They analyze configurations, network traffic, and user activity to detect potential threats and identify areas of improvement. CSPM tools can generate reports, alerts, and recommendations to help organizations strengthen their cloud security posture.
What is known about Cloud Security Posture Management?
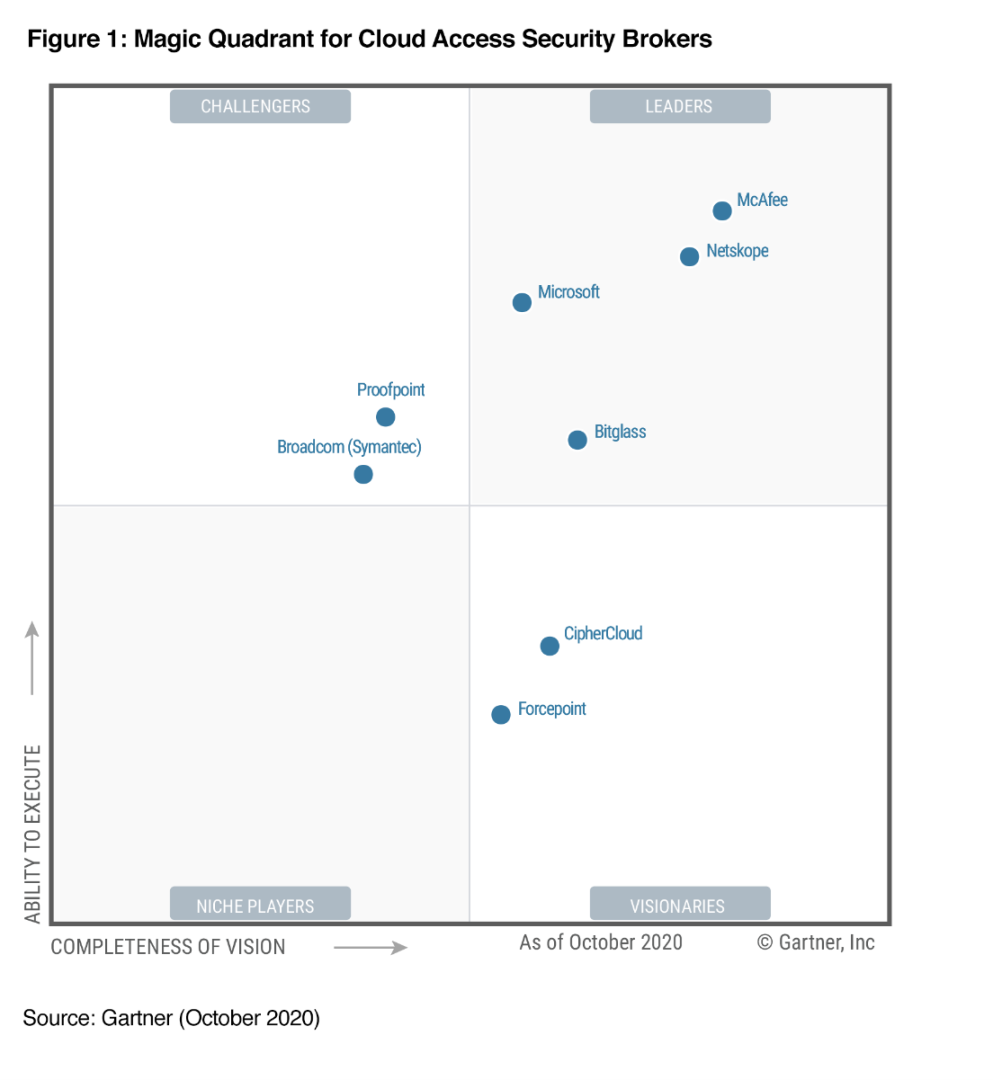
Cloud Security Posture Management has become increasingly important as organizations migrate their data and workloads to the cloud. With the growing complexity of cloud environments and the evolving threat landscape, CSPM tools play a crucial role in helping organizations secure their assets. Gartner, a leading research and advisory company, evaluates CSPM solutions in its annual Magic Quadrant report to help organizations make informed decisions when selecting a vendor.
Solution for Cloud Security Posture Management
Implementing a robust CSPM strategy is essential for organizations looking to secure their cloud environments. This involves assessing current security practices, identifying gaps and vulnerabilities, and deploying CSPM tools that can automate security monitoring and remediation. By continuously monitoring and improving their cloud security posture, organizations can reduce the risk of data breaches and compliance violations.
Information about Cloud Security Posture Management
Cloud Security Posture Management solutions offer a range of features, including asset discovery, configuration management, vulnerability assessment, and compliance monitoring. They support multiple cloud platforms, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform, and can integrate with existing security tools and workflows. CSPM solutions help organizations achieve real-time visibility into their cloud environments and address security challenges proactively.
Conclusion
In conclusion, Cloud Security Posture Management is a critical component of a comprehensive cloud security strategy. By leveraging CSPM tools and best practices, organizations can enhance their security posture, mitigate risks, and ensure compliance with industry regulations. Gartner’s Magic Quadrant report provides valuable insights into the leading CSPM vendors and can assist organizations in selecting the right solution for their needs.
FAQs about Cloud Security Posture Management:
1. What are the key benefits of using Cloud Security Posture Management?
Cloud Security Posture Management helps organizations identify and remediate security risks, improve compliance, and enhance visibility into their cloud environments.
2. How can organizations evaluate CSPM solutions?
Organizations can evaluate CSPM solutions based on their features, integration capabilities, scalability, and vendor reputation. Gartner’s Magic Quadrant report can also provide valuable insights.
3. How does CSPM differ from traditional security practices?
CSPM focuses specifically on securing cloud environments and addressing the unique challenges associated with cloud security, such as dynamic infrastructure and shared responsibility models.
4. What are some common security risks in cloud environments?
Common security risks in cloud environments include misconfigurations, unauthorized access, data breaches, and compliance violations.
5. How can organizations ensure continuous improvement of their cloud security posture?
Organizations can achieve continuous improvement by implementing regular security assessments, conducting security training for employees, and staying informed about the latest security threats and best practices.



