Cloud Based Endpoint Protection: Ensuring Comprehensive Security for Your Business
What do you mean by Cloud Based Endpoint Protection?
Cloud based endpoint protection is a security solution that safeguards the endpoints of a network by leveraging cloud infrastructure. Endpoints can include laptops, desktops, mobile devices, servers, and even IoT devices. This approach allows for real-time monitoring, threat detection, and response capabilities, all while offloading the burden of heavy security tasks from the local devices to the cloud.
How does Cloud Based Endpoint Protection work?
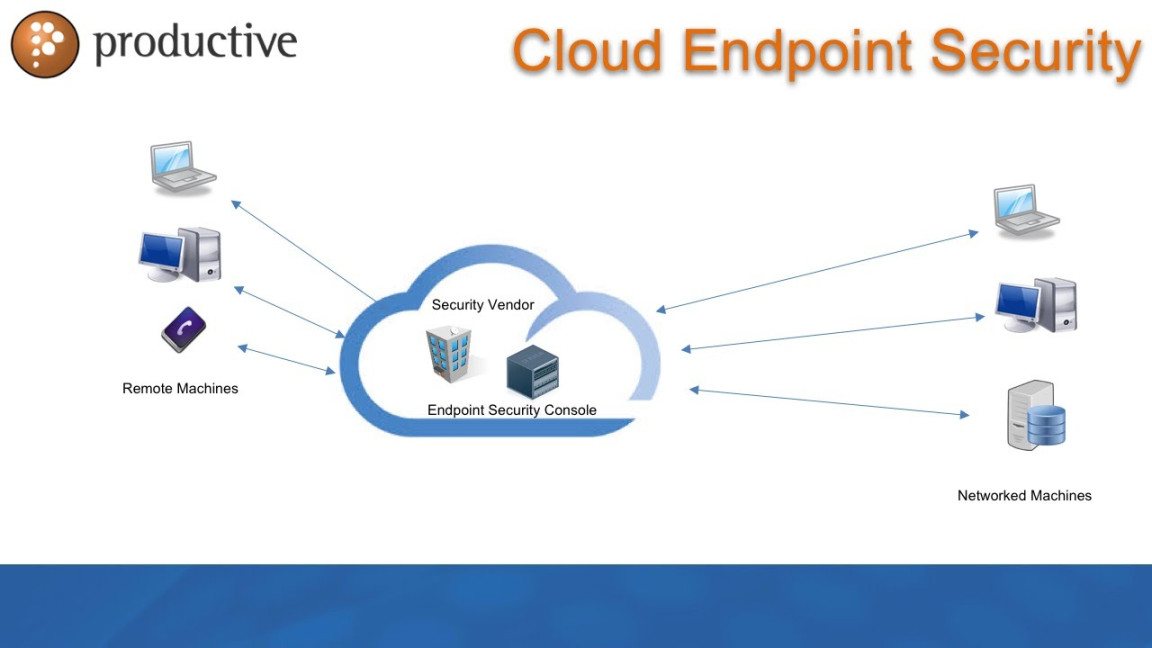
Cloud based endpoint protection works by installing lightweight agents on each endpoint device to collect data and send it to the cloud for analysis. The cloud infrastructure then uses artificial intelligence and machine learning algorithms to detect and respond to potential security threats in real-time. By continuously updating its threat intelligence database, the solution can stay ahead of the latest cyber threats and provide proactive protection.
What is known about the benefits of Cloud Based Endpoint Protection?
One of the key benefits of cloud based endpoint protection is its ability to provide comprehensive security for all endpoints in a network, regardless of their location. This means that even remote devices or mobile devices can benefit from the same level of protection as on-premises devices. Additionally, the cloud-based approach allows for automatic updates and patches, reducing the burden on IT teams and ensuring that all devices are always up-to-date with the latest security measures.
What is the solution offered by Cloud Based Endpoint Protection?
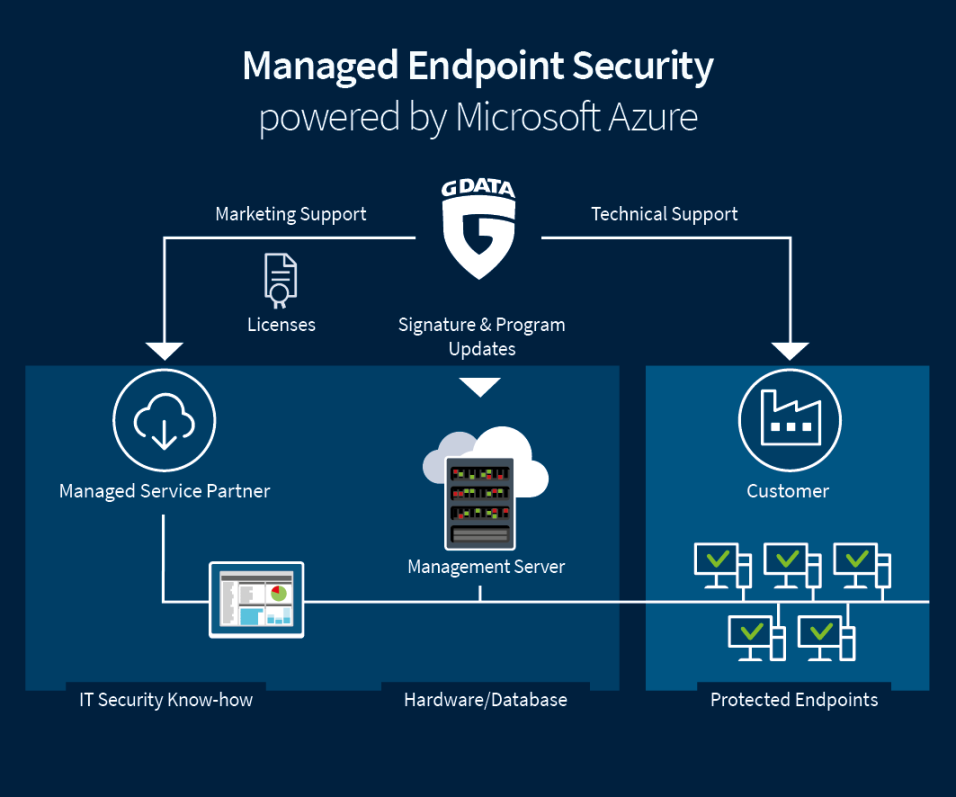
Cloud based endpoint protection offers a holistic security solution that includes features such as antivirus protection, firewall management, intrusion detection and prevention, application control, and data loss prevention. These features work together to create multiple layers of defense against cyber threats, ensuring that endpoints are protected from a wide range of attacks.
Information about the deployment of Cloud Based Endpoint Protection
Deploying cloud based endpoint protection is a relatively straightforward process. It typically involves installing the lightweight agents on each endpoint device, configuring the policies and settings in the cloud console, and monitoring the security alerts and reports generated by the solution. Some providers also offer automated deployment tools that can streamline the deployment process and ensure that all endpoints are properly protected.
Conclusion
Cloud based endpoint protection is a powerful cybersecurity solution that can provide comprehensive security for all endpoints in a network. By leveraging the cloud infrastructure, organizations can benefit from real-time threat detection, automatic updates, and proactive protection against a wide range of cyber threats. With its ease of deployment and management, cloud based endpoint protection is a must-have for businesses looking to enhance their security posture and safeguard their sensitive data.
FAQs
Q: Is cloud based endpoint protection suitable for small businesses?
A: Yes, cloud based endpoint protection is scalable and can be tailored to fit the needs of small businesses.
Q: Can cloud based endpoint protection protect against ransomware attacks?
A: Yes, cloud based endpoint protection can detect and block ransomware attacks before they can encrypt files on the endpoint devices.
Q: How does cloud based endpoint protection handle mobile devices?
A: Cloud based endpoint protection can protect mobile devices by installing a lightweight agent that provides continuous security monitoring.
Q: Is cloud based endpoint protection cost-effective?
A: Yes, cloud based endpoint protection can be more cost-effective than traditional on-premises security solutions, as it eliminates the need for expensive hardware and maintenance.
Q: Can cloud based endpoint protection be integrated with other security solutions?
A: Yes, cloud based endpoint protection can be integrated with other security solutions to create a layered defense strategy and enhance overall security posture.



