Understanding Cloud Security Systems
What do you mean by Cloud Security Systems?
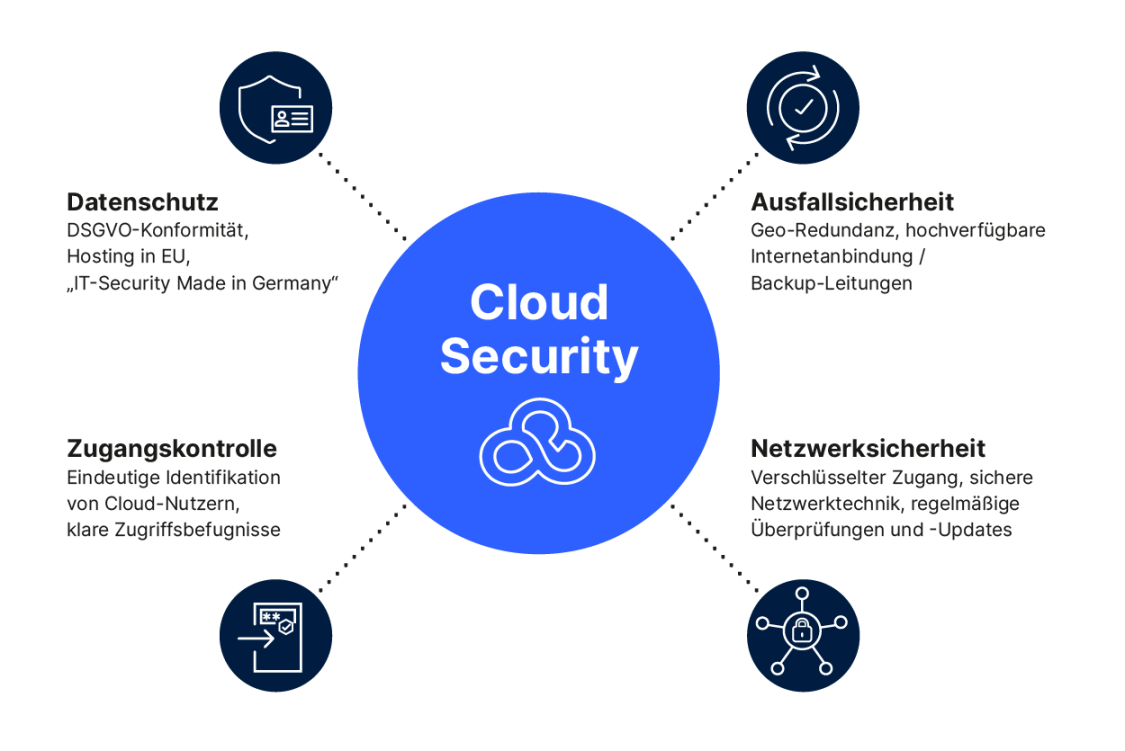
Cloud security systems refer to the practices and technologies put in place to protect cloud computing environments from potential threats and unauthorized access. These systems are designed to ensure the confidentiality, integrity, and availability of data stored in the cloud, as well as the security of the infrastructure hosting the data.
How do Cloud Security Systems work?
Cloud security systems work by implementing various security measures such as data encryption, access control, multi-factor authentication, intrusion detection, and security monitoring. These measures help to prevent unauthorized access, data breaches, and other security incidents that could compromise the security of the cloud environment.
What is known about Cloud Security Systems?
Cloud security systems are essential for organizations that store sensitive data in the cloud, as they help to protect the data from cyberattacks, data breaches, and other security threats. These systems are designed to provide a secure and compliant environment for data storage and processing, ensuring the security and privacy of the data stored in the cloud.
Solution for Cloud Security Systems
There are various solutions available for implementing cloud security systems, including cloud security platforms, encryption tools, security monitoring services, and compliance management solutions. Organizations can also work with cloud service providers to implement security measures and best practices to enhance the security of their cloud environments.
Information about Cloud Security Systems
Cloud security systems help organizations to secure their data and applications in the cloud, protect against cyber threats, and comply with data privacy regulations. These systems provide a layer of security that is essential for safeguarding sensitive information and ensuring the integrity of cloud infrastructure.
Description of Cloud Security Systems
Cloud security systems are designed to protect data stored in the cloud from unauthorized access, data breaches, and other security threats. These systems employ various security measures to ensure the confidentiality, integrity, and availability of data in the cloud, as well as the security of the infrastructure hosting the data.
Benefits of Cloud Security Systems
The benefits of implementing cloud security systems include improved data security, compliance with data privacy regulations, protection against cyber threats, and enhanced visibility and control over cloud environments. These systems help organizations to mitigate risks and secure their data in the cloud.
Challenges of Cloud Security Systems
Despite their benefits, cloud security systems also face challenges such as complexity, scalability, and integration with existing security infrastructure. Organizations need to carefully plan and implement cloud security measures to address these challenges and ensure the effectiveness of their security systems.
Best Practices for Cloud Security Systems
Some best practices for implementing cloud security systems include conducting regular security audits, implementing data encryption, using multi-factor authentication, monitoring network traffic, and educating employees on security best practices. These practices help to enhance the security of cloud environments and protect against potential security threats.
Conclusion
In conclusion, cloud security systems are essential for organizations that store data in the cloud, as they help to protect against cyber threats, data breaches, and other security incidents. By implementing best practices and security measures, organizations can enhance the security of their cloud environments and ensure the confidentiality, integrity, and availability of their data.
FAQs about Cloud Security Systems
1. What are the key components of cloud security systems?
Cloud security systems typically include data encryption, access control, multi-factor authentication, intrusion detection, and security monitoring.
2. How can organizations improve the security of their cloud environments?
Organizations can improve the security of their cloud environments by implementing best practices such as regular security audits, data encryption, and employee training on security awareness.
3. What are the benefits of using cloud security systems?
The benefits of using cloud security systems include improved data security, compliance with data privacy regulations, and protection against cyber threats.
4. What are some common challenges faced by organizations in implementing cloud security systems?
Some common challenges faced by organizations in implementing cloud security systems include complexity, scalability, and integration with existing security infrastructure.
5. How can organizations ensure the effectiveness of their cloud security systems?
Organizations can ensure the effectiveness of their cloud security systems by following best practices, conducting regular security audits, and monitoring network traffic for potential security threats.



